02 May 2018 Update – One of our oldest customers was hit by the “GandCrab Version 2” malware yesterday. The scary thing about this attack was it managed to not only encrypt the files on their server (including their Herschel data), it also corrupted their overnight online backup. So now they may have to restore their last physical backup – which is over two months old. Not a good situation.
So the message is to make regular physical backups (for example, using an external USB key or HD), as well as those made using an online backup service.
————————
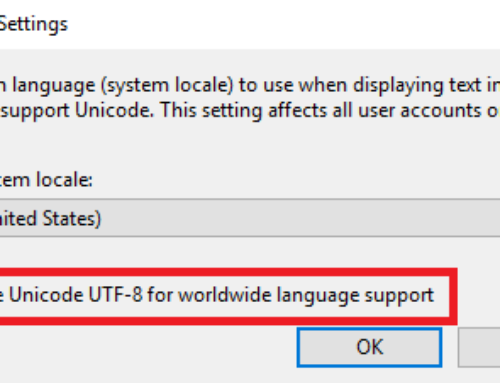
27 Oct 2017 Update – Seems like the NHS WannaCry attack could have been prevented after all. “The report said NHS trusts had not acted on critical alerts from NHS Digital and a warning from the Department of Health and the Cabinet Office in 2014 to patch or migrate away from vulnerable older software.”
————————
09 Aug 2017 Update – Here’s an interesting story about TNT which demonstrates that malware + cloud = widespread chaos. Thankfully no Herschel users appear to have been victims of this year’s attacks. But keep making those backups!
————————
12 May 2017 Update – It’s just over a year ago since I posted this article about malware. Today’s NHS malware attack (although I suspect they weren’t specifically targeted, they were just careless) demonstrates how easy it is for even giant organisations to get infected. So make sure your Herschel files are backed up! And that all your copies of Windows are updated, ideally automatically! All this malware is making us extra paranoid. We now back up continuously to the cloud and dump everything onto an external drive.
————————
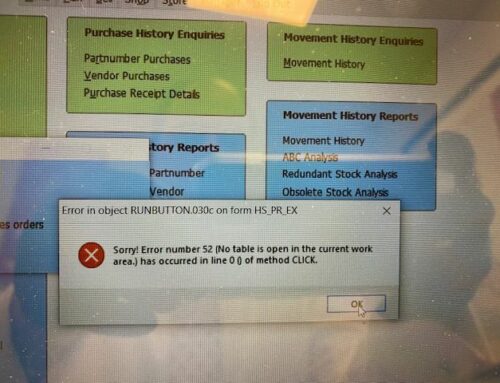
01 May 2016 – This week another Herschel user suffered a malware encryption attack. This variant was called Locky and it encrypted all their Herschel datafiles.
So that’s three attacks so far in the last year, with more to come, we suspect.
Malware of this type encrypts any files it thinks might be business-related. Unfortunately, this includes the DBF type files used by Herschel.
The only way to recover your encrypted Herschel data is from a backup. Of the three sites attacked, only one had a recent enough backup to successfully restore their data.
Please backup your copy of Herschel every day! And check your backup really can be restored!
Update 08 Jun 16 – Scary story on the BBC news website about a Canadian university paying $20,000 dollars to get their data back.
“It’s very tempting for organisations to pay out the ransom because that might be the only way they can get their data back, but that makes it worse for everyone else because it encourages more people to set up schemes like the one used in the Calgary case,” commented Dr Steven Murdoch from University College London.